Background
Insecure systems are breached by hackers at an increasingly alarming rate, and VoIP infrastructure is no exception. Companies everywhere are looking protect their communications, and currently the best possible security solution for session-based communications(mostly SIP) is to utilize a SBC (Session Border Controller).
Requirements
Reliability
Enterprise/Carriers require low-latency communications that are reliable, redundant and capable of quickly recovering from network failures.
Scalability
Enterprise Businesses, especially SME’s, require a unified low-cost platform with high-port densities capable of running various CPE-oriented applications.
Security
The critical nature of enterprise/CSP makes security a top priority.
Technological requirements include:
- Fanless and zero-noise in offices with a data center
- LAN Bypass for reliable network operations and alternative
- A performance-and-power balanced CPU programmed with built-in cryptographic acceleration technologies
- Wide compatibility and interoperability
First: What exactly does a Session Border Controller do
Session border controllers started out with one relatively simple function – as a secure entry into VoIP networks (essentially a VoIP-specific firewall) , but over the time SBCs have been extended to capitalize on edge computing applications. The essential functions can be derived and broken down from the name:
Session– Refers to the fact that it is utilized for session based communication(I.e the SIP protocol used for VoIP). In the context of VoIP telephony: a session consists of a signal/message dedicated to controlling the call, while one or more other signals carry the transmission(i.e audio, video).
Border– The fact that it sits on the border means that it has the responsibility of managing sessions between these borders.Since they sit on the edge of networks, functions like protocol translation and media stream isolation can be employed.
Controller– Dataflows from sessions are controlled and orchestrated in a SBC, hence the controller denomination.
Under these 3 main tasks fall a myriad of closely related functions, many of which include communication security hardening applications.
Lanner Presents: Carrier-class Management, QoS, Network Security
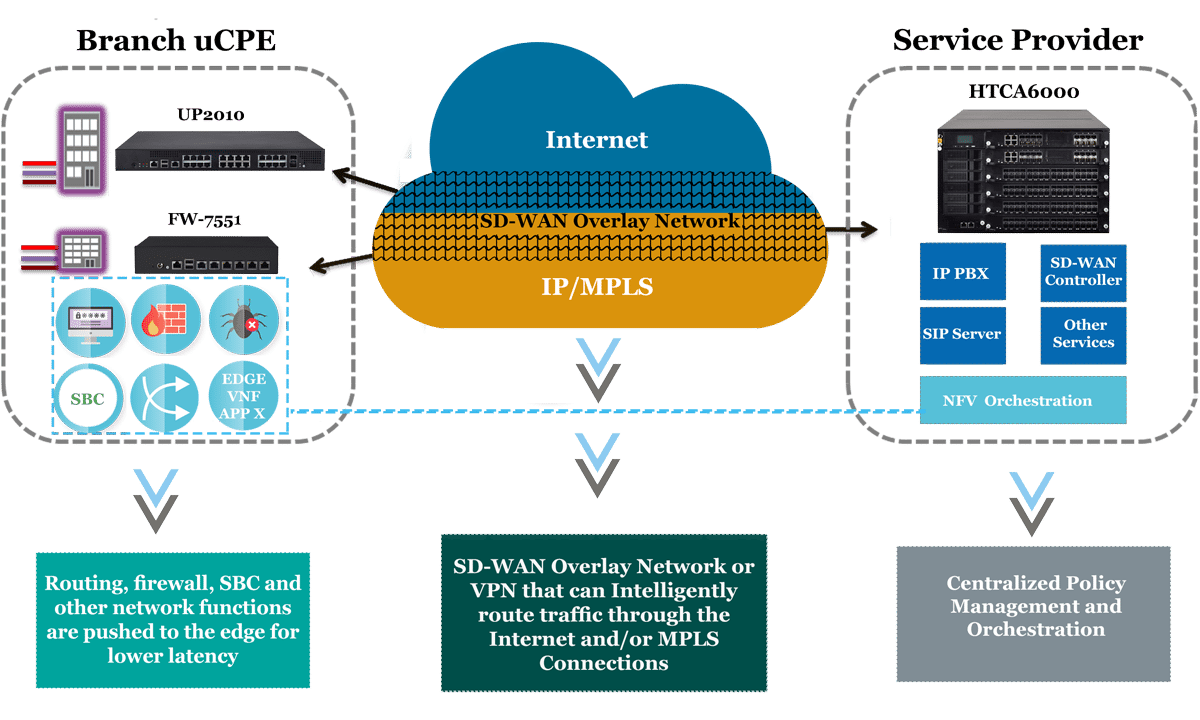 Pushing services to the cloud offers incredible benefits, and requires little hardware on the CPE side, but it introduces latency and security concerns that are unacceptable in enterprise networks .
Pushing services to the cloud offers incredible benefits, and requires little hardware on the CPE side, but it introduces latency and security concerns that are unacceptable in enterprise networks .
With lanner extensible x86 uCPE hardware platforms, Virtual SBCs, Firewalls and other network functions that operate more efficiently on the edge can be appropriately deployed.

Lanner’s FW-7551 can be considered a value compact desktop appliance due to its rich functionality and network redundancy design. The fanless desktop network appliance utilizes Intel Atom™ C2000 Series Processors, including dual-core C2358, quad-core C2518 or C2558 (Codenamed “Rangeley”), to deliver multi-core performance and built-in Intel QuickAssist crypto acceleration technology. The hardware-assisted crypto accelerator helps secure enterprise networks. For connectivity redundancy, FW-7551 comes with 6 GbE RJ-45 LAN ports, featuring 1 pair LAN bypass functionality to ensure network operation when interruption occurs. For wireless network, FW-7551 supports an internal mini-PCIe socket that supports both PCIe and USB signals for wireless network cards.

Lanners Carrier-grade cloud computing HTCA 6600 platform is built using industry standard commodity x86 Intel Xeon components. This platform was made envisioning the software-defined age with network virtualization providing the greatest flexibility to date. Designed Using a modular approach to provide a clear, cost-effective upgrade path to today’s ever-growing demands, available with up to 2x switch blade modules and 4x Ethernet 10Gb/32 SFPport with 6x CPU blades housing dual Xeon E5-2690 v3/v4 sockets. This cloud computing appliance provide the Price:Performance that carriers and large enterprises require for a software-defined shift.