Abstract
IoT targeting malware is evolving at a rapid pace, and as the healthcare industry continues to leverage embedded computing & networking technology, so do hackers. Ransomware has steadily changed over the years, starting off as software that literally holds the device itself for ransom, disabling functionality and hindering operation. With the advent of powerful encryption and CPU’s, the software evolved into a malicious file encryption ransom scheme.
Now, with IoT permeating healthcare in everything from patient monitoring systems, to EHR (Electronic Healthcare Record) systems, opportunistic hackers are changing their game once again. Due to the critical nature of the healthcare industry, and the fact that security has evolved to counteract data-stealing ransomware, malware authors are falling back on the old scheme – holding the devices themselves hostage.
Problem
Cyber Security is an ever-increasing concern in the healthcare industry. Last year over 15 ransomware attacks successfully breached systems, with significant number of them resulting in a begrudging payout.
Legacy Systems
The healthcare industry is plagued with outdated and vulnerable systems – running on software the likes of windows XP. We are talking about extremely expensive machines (X-ray, MRI etc.) which came out over a decade ago and have long since had no support; replacing all of these machines will be far too costly in most cases.
BYOD Attack Vector
By popular demand, and perceived company benefits (lowered CAPEX on hardware, employee off-time use), bring your own device environments are likely here to stay. This introduces new security concerns for enterprise networks, as automatically provisioning, configuring and containing these unknown devices will be easier said than done.
More than half of attacks start as a simple email or social media messages. Once the questionable link is clicked, vulnerabilities in word document macro codes, browser javascript or adobe PDF’s are exploited by malware to gain access to the machine, and ultimately the network.
Solution
Lanners powerful NGFW appliance: FW-8896, a dual socket Intel Xeon based, DPDK ready appliances that provides enough computing power to analyze packets at the application layer (7). This allows for comprehensive screening and machine learning techniques to be employed at the edge of the network, blocking unwanted content before it hits internal network.

NGFW is one key piece of the puzzle, as well as the first and most powerful line of defense in a modern network. This protection ends at the network edge however, and as much as security professionals would love to stop malware hitting the internal network, sometimes that’s simply impossible (0day exploits, sabotage, internal conflicts) .Good thing Hackers aren’t the only ones that can employ old techniques for new problems.
Enter Network segmentation
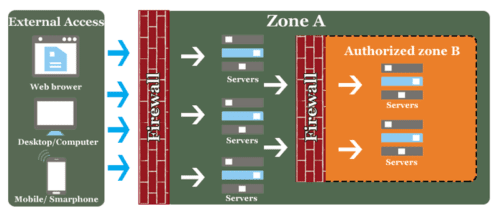
Also known as a DMZ (Demilitarized zone), these are isolated areas of a network that have a firewall appliance in between the only network ingress/egress point. This effectively creates a tightly controlled zone accessible only to those allowed through said firewall. By implementing security through compartmentalization, techniques like end-to-end encryption can start to shine through.

Lanner’s FW-8893, a High Performance 1U Rackmount Network Security System with up to 2 Xeon E5-2600 v3/v4 CPUs, 128 Gbps I/O and redundant Power Supply. Internal networks operate at a much faster speed, Lanners high-capacity security appliance running on 2 Intel Xeon x86 CPU’s will be more than powerful enough to secure a large network zone, at line-rate speeds. Capable of running network monitoring software, IDS/IDP, web filtering, security policy enforcing, and network access control technologies to bring real-time security analytics to the healthcare industry.





