Concepts
Encryption
Plaintext communications are inherently insecure from prying eyes, that’s why encryption is used to transform sensitive information into unreadable messages which can only be deciphered by the keyholder(s).
Encryption Types:
Symmetric: symmetric encryption algorithms use the same key for encryption and decryption. Any computer with access to this key can decrypt and encrypt messages.
Asymmetric: asymmetric encryption utilizes separate keys for encryption and decryption. Also called public-key cryptography. This is useful in, for example, app distribution- where packages are signed by a trusted distributor and decrypted by end-users with the readily available public key.
Authentication/Authorization

When a client or a server needs to identify exactly who is accessing the resource/site, several authentication techniques can be used. To authenticate, one has to provide solid proof of identity to the server/client; there are several ways to do so, the prominent one being user/password authentication.
Other types include:
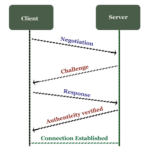

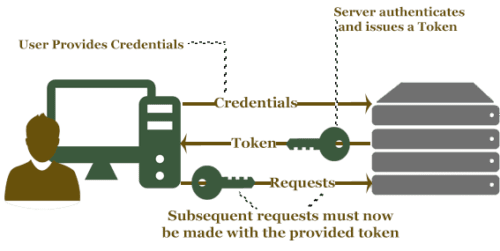
Once authenticity is established, systems can use authorization to determine what resources it can access. Moderns systems employ a combination of authentication/authorization to not only determine who is accessing but control what they can access.
DoS /DDoS
Denial of service attacks works by overloading/crippling key systems that are critical to service. Given the growth rate of technology, overloading servers/firewalls have necessitated increasingly larger network resources. This has given way to the now widely employed DDoS attacks, or distributed denial of service.
In a distributed denial of service attacks, malicious entities utilize numerous internet connections and machines to carry out massive attacks that can cripple even the most equipped services. Considering the scale of some of these attacks, botnets are the preferred method to acquire these resources. Hackers take control of unsafe computers, devices and more recently IoT devices; they use automated scripts that scan ports for vulnerabilities, brute force default passwords (IoT devices are a major culprit of this).
Defending against these types of attacks is extremely difficult, given the nature of the attack. The traffic can appear as normal user-generated traffic, so any attempts at filtering it can lead to harmful impacts on legitimate users. Special anti-DDoS systems are available that can mitigate these attacks, but even they can be overloaded with enough traffic. The only real solution is expensive powerful hardware that can handle these huge bursts of traffic
Technologies
Firewall
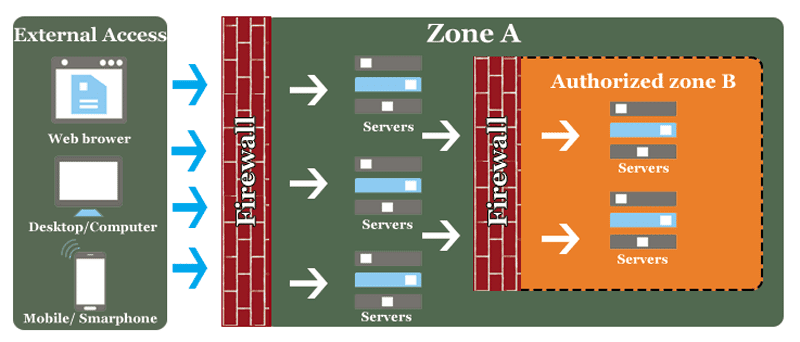
Nowadays most people have heard of a firewall, but many don’t really know what its functions are. A firewall in practice is a layer between the internet and LAN’s. Because of the open nature of the internet, any hacker could potentially find vulnerabilities in your networked machines. To mitigate such intrusions firewalls are erected to help defend against unwanted intruders.
Firewalls can be divided into 3 generations: Packet filtering, Stateful and application level.
Gen 1 – Packet filtering
The first generation of firewalls was based on a set of rules given to a packet filter, the filter then governs which packets should be allowed in(and out) of which ports, and what shouldn’t. If the packet passes the filter rules it’s allowed through, if not it’s either dropped silently or dropped along with an error message transmission.
Packet filtering works at the lowest levels of the OSI network Models, with a small use of the 4th layer (Transport) to determine things like originating IP and port destination information. It filters things by port, by transport protocol type (TCP, UDP) and by originating IP.
Gen 2 – Stateful filters
These firewalls make full use of the 4th player in the OSI model layer to perform stateful packet inspection. Stateful refers to the fact that it can determine the state of a network connection and use it for filtering purposes. It accomplishes this task by using a different packet inspection technique. Instead of looking at individual packets as they come in, it collects enough packets to determine the connection and traffic before letting the packets through, this allows the firewall to analyze the state of a connection and verify if a packet belongs to a given connection.
Gen 3 – Application layer
These firewall work on all 7 layers of the OSI model, as such they require relatively massive amounts of computing power compared to the previous two generations. The usefulness in application-level filtering is that firewalls can determine and understand which applications and protocols are in use (i.e. FTP, HTTP). This can be used to mitigate and thwart connections from unknown/malicious applications that are trying to bypass generation 1 &2 firewalls using permitted ports/protocol combinations. Today, next-generation application layer firewalls all work in similar ways, by using deep packet inspection to extend functionality to the application layer, a system such as a WAF (web application firewall), IDS/IPS can be achieved.
IDP / IPS
Intrusion Detection System
To easily differentiate between a firewall, think of an Intrusion detection system as the added layer of security after a firewall. It serves to protect an internal network once an intruder has bypassed external defenses. IT takes many forms from many vendors, but they all essentially work by monitoring all the traffic in the internal network and looking for suspicious, unwarranted activity.
Intrusion Protection System
These are usually added as functionality to IDS, where intrusion detection systems serve to detect, intrusion protection systems serve to act against the intruder. Once the suspicious activity has been detected, the information is feed into the IPS, where it performs appropriate actions to secure vulnerable/targeted assets.
VPN
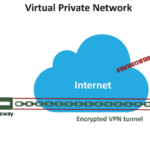
A virtual private network is an overlay network (with optional encryption) that runs on top of existing network infrastructure. Many enterprises and power users use it to secure communications between endpoints by sending all traffic through an encrypted tunnel.
Proxy
A proxy server or application gateway is colloquially known as a “proxy“.
Functioning essentially as a middleman/gateway between a local network (home LAN, corporate intranet) and larger-scale networks such as the internet.
They are used to provide an added layer of security, anonymity, and performance.
Internet data transport security Protocols
For securing communications in everyday web browsing, several protocols exist which allow encryption in communications. These are easy to see in uses: it’s the ‘s’ that appears after https, which signifies the use of one of these secure communications protocols.
SSL and TLS are both very similar protocols for enabling secure authentication and data encryption between computers, servers, and applications. They both provide easy ways for internet browsers to use encrypted communications for transmitting sensitive data.
SSL: Secure sockets layer a prominent implementation of a public key encryption system. SSL SSL is now officially deprecated due to several vulnerabilities.
TLS: Transport layer security is the current standard and successor to SSL.
Types of Cyber Attacks
Cyber attacks are defined as an attempt by a hacker or hackers to gain unauthorized access to, steal from, damage or destroy a computer system or network. let’s take a look at some of the different types.
Phishing:
A phishing attack is typically defined as an attempt by hackers or fraudsters to impersonate a business and trick you into giving out sensitive or personal information. Usually, these types of attacks come in the form of an email that will contain a link enclosed. When users click this link they will be redirected to a fake site that will attempt to steal their details. In some, more advanced, cases, merely clicking the link is enough to install malware on a system and give access to your data and files. Protecting yourself against phishing attacks mainly comes down to being security savvy and being able to spot potentially fraudulent emails.
Malware:
Malware can be viewed as a collection of different cyber-attacks including viruses and ransomware and is roughly defined as malicious code with the intent on stealing or destroying something on a computer or network. Once, ransomware, for example, is uploaded or downloaded onto a computer, it immediately encrypts the user’s hard drive and files and proceeds to demand a cash sum for their release. There are also no guarantees that, should the user pay the demand, they’ll get their files or computer back. Protecting yourself from malware uses much of the same logic as protecting yourself from phishing emails. Spam links and ads may seem tempting but, as with most things, if something sounds too good to be true, it is, and it’s probably malware too.
Worms:
Cousins of the traditional computer virus, network traveling worms don’t pose as much of a threat as they once did, however, that doesn’t mean they can’t still wreak havoc on an infected network. Famous examples include Conflicker and Zeus the latter of whom was spread using phishing methods to send messages through Facebook and email. Worms are another example of how being clued-up when it comes to cyber threats can help prevent exposure to this and other types of malware. Suspicious links in emails from anonymous senders are a big clue that something isn’t quite right. And if you do end up opening an email or clicking a link, report it immediately so attempts to mitigate infection can begin.
Password Attacks:
Password attacks are attempts by hackers to crack your password and they come in a number of different forms. Brute Force attacks use automated software on the hacker’s own system to produce huge numbers of guesses while others use software that could try to use different popular word combinations. As you may have guessed, strong passwords are the best way to protect against these types of threats. Passwords such as “1234567890” or “Password123” are weak attempts at protection and will most likely be featured in any hacker’s password cracking software.
DOS Attacks:
Denial-of-Service attacks attempt to disrupt and overload the service to a specific network. They usually consist of an attacker taking control of a large number of machines and using them to send vast amounts of traffic or data through the target network. This overload of connection requests causes the disruption to network services and can have huge impacts on businesses online access and services should the fall victim to one. Regular maintenance and patch updates to a modernized, upgradeable security system are one of the best ways to avoid DOS attacks, however, most modern attacks of this kind are largely aimed at international corporations and governments, usually in protest of a civil or political issue.
DDOS Attacks:
Distributed Denial-of-Service attacks are a type of DOS attack where multiple systems infected with Trojans (Usually RAT Trojans, more on those later) are utilized in order to target a single system. Attackers will often have infected large numbers of computers and systems with malware that will then allow them to manipulate and control the network or device. Once the attacker feels they have a large enough collection of infected systems (a botnet) to begin, the attack begins. The difference between a DOS attack and a DDOS attack mainly comes down to the numbers involved. DOS attacks typically use only a single computer to attack their target, whereas a DDOS attack takes advantage of large numbers of infected systems and combines them to target a single computer or network.
MITM Attacks:
Man in the middle of MITM attacks look set only to increase as the Internet of Things enables further connectivity with our smart devices and vehicles as they also become more widely available. MITM attacks involve a man in the middle impersonating the endpoints in online information exchange and intercepting information from both entities involved in the exchange. These attacks can be particularly damaging, for example, if the MITM is impersonating your bank in an online exchange as you risk unknowingly handing over your sensitive financial information to a hacker. Using only encrypted, WPA or greater access points can ensure relative safety from these kinds of attacks.
SQL Injection Attacks:
SQL stands for Structured Query Language and is a programming language used for communicating with databases and is used by many of the servers holding essential data for websites to manage the data in their databases. SQL attacks work by specifically targeting these servers in order to get them to produce information they would usually be protected by entering or “injecting” customized code. SQL servers that are vulnerable to injection attacks can be extremely problematic as data such as credit card information, personal details and more can all be made available to hackers for malicious purposes such as theft, defamation or blackmail.
Remote Access Trojans:
Remote access trojans or RATs are types of malware that include a backdoor for remote access to an infected computer or network. As with most other types of malware, remote access trojans can come in the form of emails and links as well as being downloaded invisibly in the background along with something the user themselves has chosen to download (a game, music, etc.). Once they’re on the now infected system, the hacker could choose to try and infect other systems from the one it currently occupies in order to create a botnet that could then be used for other malicious purposes such as DOS attacks.
Logic/Time Bombs:
Logic and time bombs are malicious software that is designed to cause damage to a computer or network after certain system conditions are met or after a certain amount of time has passed. Logic bombs have been known to be used as blackmail devices in the corporate world. An example would be an employee who sets up a logic bomb to go off in his employers network if he doesn’t log in for 21 days as he feels he may be fired, once the employee is actually fired, he used the logic bomb to financially blackmail his employer into paying him to disclose its location. In order to best deal with logic or time bombs, regular back-ups of a system can help to lessen the damage caused if one ever were to happen.