Introduction
It is believed that as enterprises adopt cloud, Edge and mobile computing, almost half of these enterprises have suffered one or more hacking attempts or actual network breaches. Furthermore, more than 22,000 new security holes were disclosed over these past couple of years, and over 1/3 of these network loopholes exhibited an exploit available.
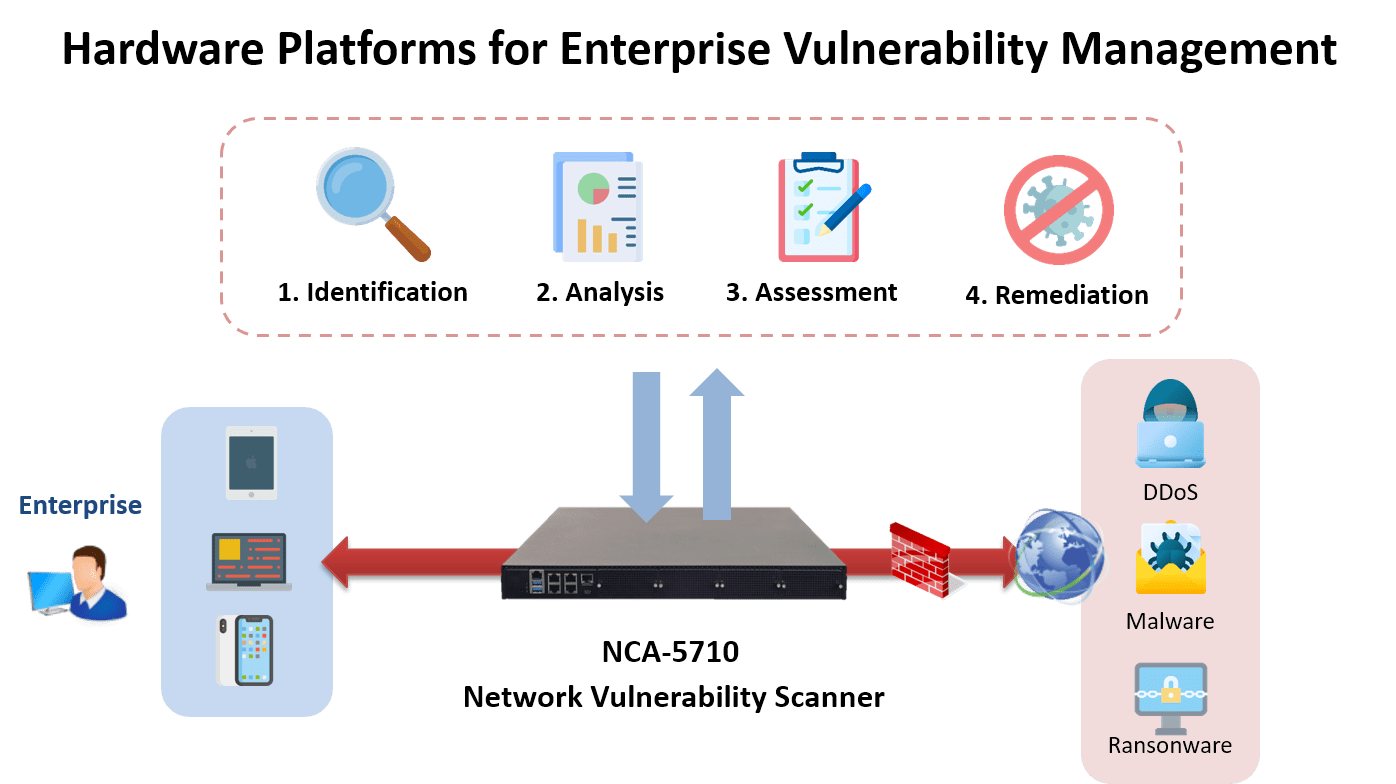
Network vulnerability management therefore is vital to endpoint security and is one of the most proactive approaches organizations must adopt in order to weed out security weaknesses before they lead to a breach.
Challenges / Requirements
A leading provider specializing in developing security risk management solutions came to Lanner in search of a capable hardware appliance on which an all-in-one proprietary network terrain analytics application could be run so that the said SaaS could be delivered as a complete network vulnerability management package.
The hardware appliance must be sufficiently robust and powerful in order to make available the following functionalities:
– Identify and catalogue unscanned assets
– Recognize network devices and access rules obstructing scanning access
– Deliver a visualized inventory of all reachable assets
– Detect vulnerability and misconfiguration in real-time
– Prioritize high-risk vulnerabilities by risk levels and business impact
– Deploy patching and remediation
Lanner Solution
The NCA-5710, powered by 2nd gen Intel® Xeon® Processor Scalable Family and Intel® C627 or C621 chipset, features optimized computing power and virtualization capacity in a compact 1U form factor with dual LGA3647 CPU sockets, 4x NIC module slots and up to 384GB DDR4 system memory.
This platform delivers a multitude of advanced networking features for maximizing packet processing efficiency and cryptography acceleration.
Benefits
By way of Lanner’s NCA-5710, this provider was able to seamlessly integrate network context into their enterprise network vulnerability management solution, enabling risk-based vulnerability assessment and prioritization.
All scanned data are compared with a continuously updated inventory and the map of your network, greatly facilitating the identification of assets prime for scanning.
What’s more, this all-in-one network vulnerability assessment solution makes available risk scores that are calculated using vulnerability severity and asset value of a network’s upstream and downstream assets so that network vulnerability managers are armed with enough information when proactively identifying and mitigating the vulnerabilities that would most likely lead to loopholes and breaches.
The NCA-5710’s hardware performance is capable of unifying all elements of the said proprietary vulnerability management program so that system continuity and workflows are met with minimal impact.
Result/Conclusion
The resulting product is a robust risk scanning and management solution that identifies, categories, assesses network hardware/software assets for security risks and applies the most up-to-date threat intel analysis for prioritizing actively exploitable vulnerabilities in order of risk-level and business impact.
All found loopholes are either automatically remedied with the latest superseding patch or flagged for further mitigation.
In conclusion, Lanner’s NCA-5710, a high performance network vulnerability scanning appliance, significantly boosts all businesses’ ability to proactively discover hardware/software assets’ vulnerabilities and have them mitigated before they can be exploited.
