
Background
Data breaches are usually intentional leaks of information without authorization, normally by hacking actions. Data breaches are destructive nightmares to major corporations and organizations because it severely damages not only their profitability, but also trust and reputations. Victims are usually giant corporations or organizations with huge base of users or member, which means gigantic amount of data as the target for hackers. In fact, some user or member data are highly sensitive or confidential and this will severely ruin the serviceability and reliability of the service providers.
Major incidents include well-known dating sites, multinational financial institutions, and large e-commerce websites, which millions of users data such as personal information, credit/debit data, names, passwords and profiles were reported leaked or stolen. In fact, most of the incidents took quite long to discover, but once discovered, the outcomes are usually catastrophic to reputations and sense of security. For instance, in 2013, the giant e-commerce corporation Target Corp was infiltrated with data breaching malware that stole 40 million credit card and debit records, and also around 70 million of personal information. Not only the financial losses, Target Corp had to deal with the public relation and legal issues, which would take years to recover the reputations.
Prevention Measure
Most incidents indicated that data breaches aim at the data rather than hardware infrastructures as data is the most valuable source for profitability and trustworthiness. Many corporations and institutions in the world have implemented some control solutions to protect themselves from breaches. The technological requirements of a true solid protection shall include the following in order to effectively achieve the sense of security:
Powerful architecture
- No matter how well the software is programmed, it has to be backed by a powerful hardware architecture to communicate and impose strict controls and instruction policies across all implemented network devices.
Access control
- There are many access control tools but still a well-designed architecture to run the tools efficiently.
Authentication
- Authentication procedures must be executed strictly and effectively.
Encryptions
- Data encryption is mandatory to prevent data from being stolen. High-reliability and high-availability
High-reliability and high-availability
- Prevention measures must run on an automotive, 24/7 basis so that the solution must achieve high reliability and high availability.
Lanner’s Hardware Solutions
To defend against data breaches, a powerful hardware platform is needed in order to run all the required measures in an efficient and effective manner. Lanner’s NCA-5510 is a high-performance 1U rackmount network appliance utilizing Intel® processor E5-2600 v3 series with Wellsburg PCH, codenamed Grantley. The adoption of this platform aims to deliver supreme network performance. With Intel® Grantley, NCA-5510 supports registered DDR4 memory at 2133 MHz frequency and capacity up to 256GB. This will help maximize virtualization throughputs and next-generation firewall/UTM/IPS applications. With the architectural benefits and advantages, NCA-5510 delivers optimal throughputs in conducting security instruction policies to run authentications, access controls, and encryptions.
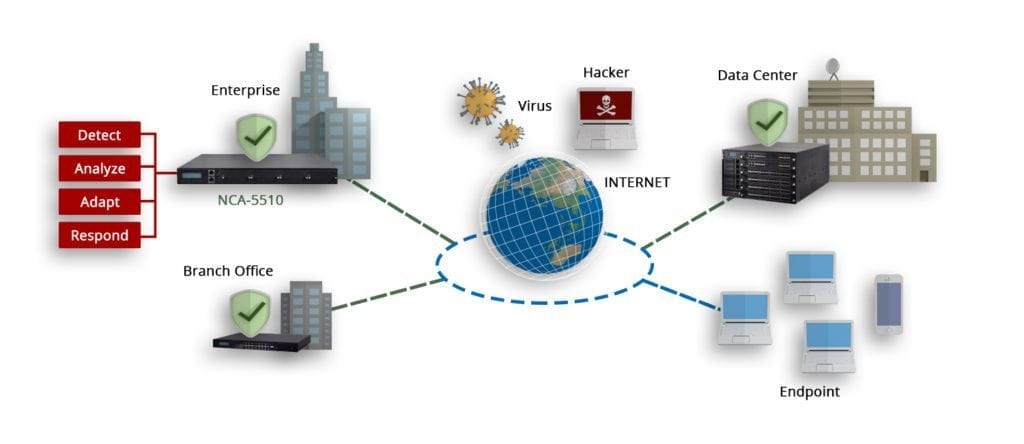
The expandable scalability and I/O flexibility make NCA-5510 the ideal deployment for enhancing network traffic management and virtualized network security. NCA-5510 offers high-port density by delivering up to 32 GbE RJ-45 ports in just 1U form factor. High throughput and crypto acceleration expansions are scalable through 4 slim type module slots, supporting 40G/10G/1G/Fiber/Copper/Bypass/cryptographical specifications.
- NCS2-IQM201 (2-port 40G Fortville)
- NCS2-IXM407 (4-port 10G Fortville)
- NCS-IGM427 (4-port 1G with Cave Creek acceleration)
- AV-ICE02 (Coleto Creek Acceleration Card)
Other significant hardware features include NAND Flash storage, 1 x 3.5”/2 x 2.5” SATA HDD/SSD bays, 1+1 ATX redundant power at 300W and optional TPM support. With the I/O advantages and scalability, NCA-5510 presents high reliability and serviceability in running data breach protection measures.
