
Background
A report released by U.S. Energy Department suggested that the number of cyber attack incidents already reached the “red-alert” level, which also indicates how vulnerable the security is for today’s critical infrastructures. In fact, besides the common targets for hackers such as power plants and manufacturing sites, there was a reported incident in 2016 that a water company in U.S.A experienced data breach.
The vulnerability was quite astonishing, as critical infrastructures are the sources of utility that we rely on everyday. The report discovered that the OT (operational technology) server at the victimized water facility was outdated, and hackers intruded through and managed to control hundreds of PLCs (programmable logic controllers). The hacker or hackers even accessed to the software of the PLCs that can adjust the setting of chemicals treatment for the water. Thus, the recovery of water supplies was delayed.
This incident showed that the OT protection in infrastructure requires a more updated, and more robust approach to ensure serviceability for the public.
Requirements
An expert in Middle East specialized in OT networks and SCADA cyber security for critical infrastructures worked with Lanner to come out with a robust server that can perform reliably in harsh environment and wide remote monitoring for multiple water facility networks. The collaborated robust server meets the following technological requirements:
DIN Rail Mount
DIN Rail mounting is widely used in ICS settings, such as equipment racks. Thus, a DIN Rail mounting must be designed for the server.
IEC/IEEE Compliance for harsh environment
Critical infrastructures are mostly situated in remote, unmanned harsh environments with possible electrical surges or other uncertainties. Thus, the demanded solution shall be compliant with IEC61850-3 and IEEE1613 to ensure reliability.
LAN Bypass mechanism
LAN bypass is a necessary fault-tolerant mechanism especially for systems deployed in unmanned, harsh environment. In fact, the demanded server shall be integrated with the latest LAN bypass technology to ensure stability in network traffic.
Designed for wide temperature operation
Extreme ambient temperature may occur in critical infrastructures. Thus, the required solution must support wide range of operating temperature from -40ºC to 75ºC. Physically, the system shall be in fanless design so that no mechanical part replacement is needed, and less noise.
ESD/Surge Protection & Magnetic Isolation Protection
Since uncertainty may occur with the power and magnetic in unmanned critical infrastructures, the demanded server must be equipped with ESD/surge protection, as well as 1.5KV magnetic isolation protection to minimize potential interruptions.
Dual power path with trigger alarm
The ideal power input options are in the range of 12V~48Vdc. Thus, the demanded server shall be able to connect two power inputs for backup supply with triggering alarm.
Lanner’s Solution
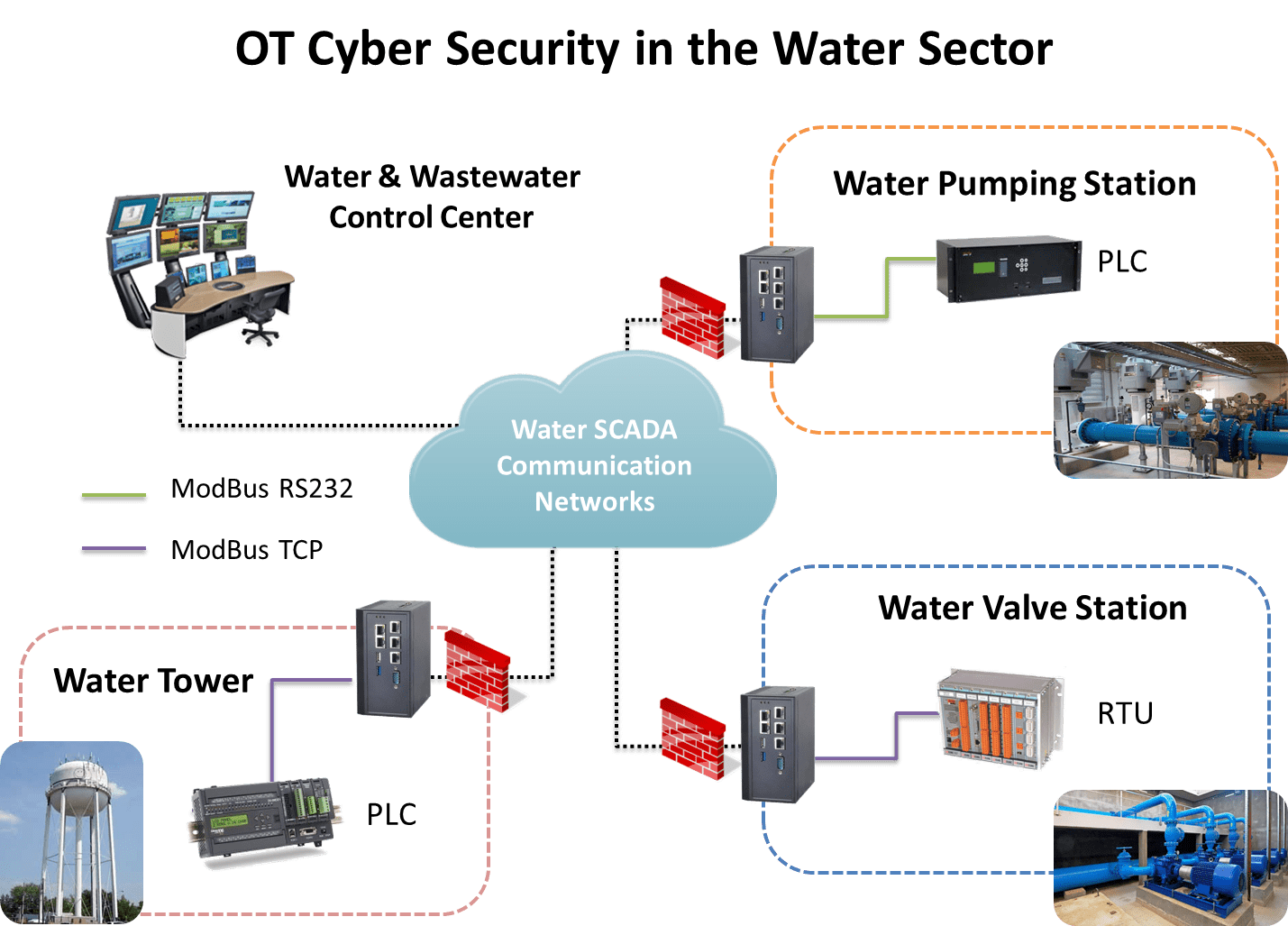
Lanner’s LEC-6032 is presented as the industrial cyber security server in water and wastewater SCADA networks. The LEC-6032 product family, is designed for OT network protections to connect with SCADA, HMI, PLC, RTU and sensors.
They use LEC-6032 Series as their industrial cybersecurity hardware appliance. They install one LEC-6032 for each pool to perform SCADA and remote terminal unit. In this application scenario, LEC-6032 is installed for each sector: water/wastewater control center, pumping station, water tower PLCs, and water valve system RTUs.
LEC-6032 offers all the required I/O connectivity for OT environment, including dual power inputs, USB, isolated COM (mainly RS-232) connectors and multiple RJ-45 and SFP networking ports.
Designed for remote, unmanned and harsh environments, LEC-6032 supports extended operating temperature from -40 ºC to 70 ºC and comes with DIN Rail mounting mechanism. In case of LAN connection failure, LEC-6032 supports one or two pairs of RJ-45 ports with LAN bypass function.
