
Background
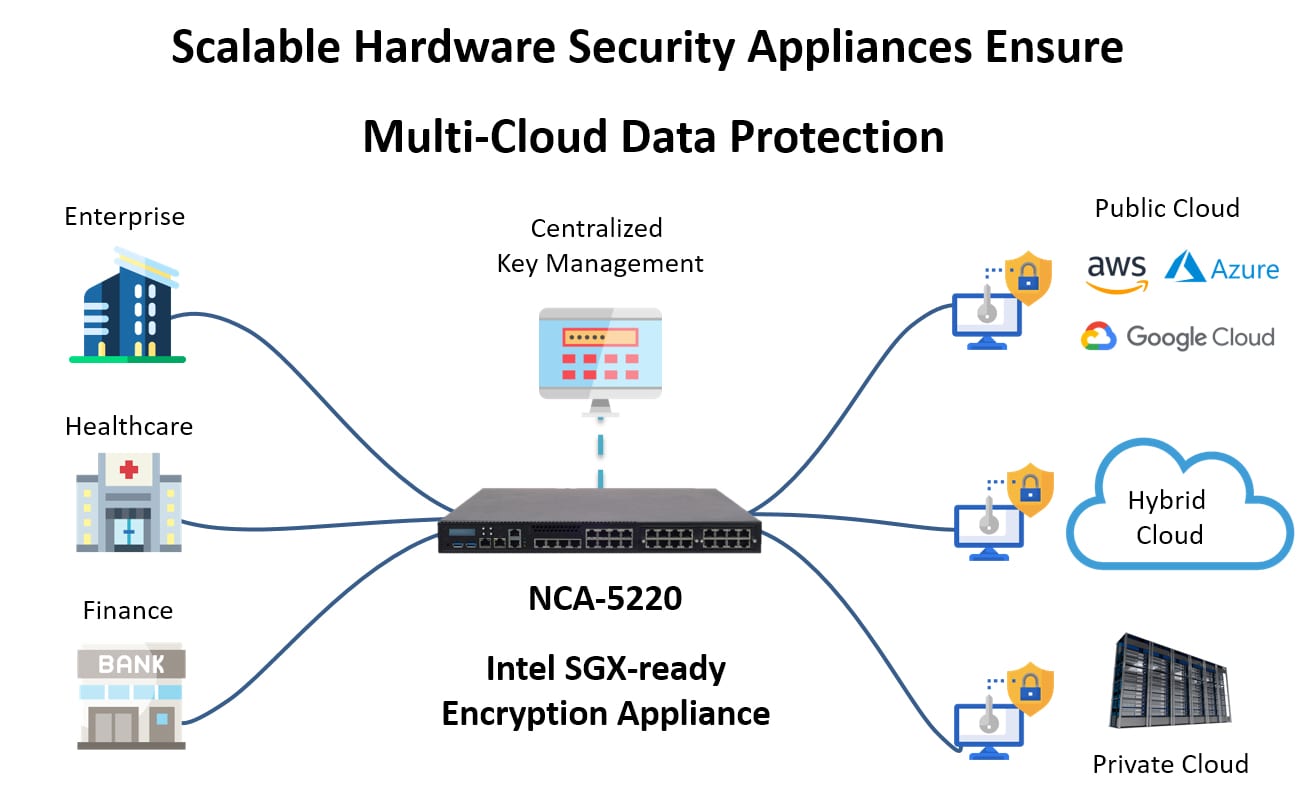
Corporations are amassing vast amounts of data, ranging from highly confidential financial, business, and customer data to moderate unimportant information. In order to augment their internal datacenters, businesses are also moving more and more of their data to the cloud and adopting multiple hybrid cloud storage environments. As such, organizations are discovering the complexity, increased costs and security risk of protecting all their data across multi-cloud environments.
Through utilizing confidential computing, organizations can protect data in-use, by encrypting workloads during operation, to avoid the risk of unauthorized access and malicious attacks, and build cross-cloud data applications from multiple parties. Additionally, confidential computing allows data to be transferred between different cloud environments without exposing confidential data to unauthorized parties. It has become increasingly important to keep high value assets such as storage encryption keys and tokens, sensitive data, and intellectual properties protected to encourage organizations to leverage cloud computing deployments and store their confidential workloads.
Requirements
New technological developments – in chips, software, and cloud infrastructure, makes it possible to manage all the data, including encryption keys, intellectual property, sensitive information between multiple hybrid, public and private clouds through a single platform. A platform that can optimize performance, control costs, enable complicated mixes of applications, while also scale and cluster between multiple sites, to achieve higher reliability and business continuity.
In addition to the critical confidential computing capability for data security, the platform must also have additional hardware security, scalable hardware design, and most importantly, advanced bypass capabilities and redundant power supply to ensure continuous network traffic throughput.
A leadingmulti-cloud US security company worked with Lanner to design such a security platform that would meet their needs and provides the following highlighting features:
- Multi-Core Computing Power – Intel® Xeon® E or Core™ i3 or Pentium® or Celeron® Processor (Codenamed Coffee Lake) for optimal performance.
- Built-in Hardware Security – Intel® Software Guard Extensions (Intel® SGX) offers hardware-based memory encryption for isolating specific application code and data in memory. Additionally, Trusted Platform Module 2.0 (TPM 2.0) provides integrated cryptographic keys and secure boot to protect the platform from unauthorized access.
- Scalable Hardware Design –F.A.S.T. N.I.C. support for 1G/10G/40G/100G Ethernet speeds in one or more modular slots where modular kits can be retrofitted via either a copper or fiber interface.
- Advanced LAN Bypass – Bypass capability that allows for uninterrupted network traffic. When an in-line networking appliance suddenly shuts down or crashes, traffic throughput will be maintained. Lanner’s design engineering has achieved improvements over typical bypass capability to enable higher reliability and greater control.
- Redundant Power Supply –Prevent network service interruption with highly reliable redundant power supply, critical for enterprise and financial networks.
Solution
Lanner’s NCA-5220 is a 1U rackmount network appliance with powerful Intel® processor for demanding network applications. The platform integrates Intel® SGX extensions toenable confidential computing for data protection and encryption, which is essential for hybrid multi-cloud networks.
This platform delivers advanced networking features with flexible configurations for LAN ports, NIC expansion, storage and management. NCA-5220 is an ideal solution for network traffic security, multi-cloud computing and data centers.
