
Background
After a series of high-profile cyber security incidents on critical infrastructures, governments and enterprises of such facilities have taken malwares seriously into considerations. Apparently, the malwares or ransomware over the past couple years, such as Stuxnet, WannaCry and Crash Override, have publically exposed the vulnerability of SCADA Networks or Industrial Control Systems in today’s power grid automation, petroleum sites and other critical infrastructures.
The vulnerability can be analyzed as a loophole in the convergence between the two technological paradigms: IT (information technology) and OT (operational technology). The IT today is long-established, and consists of open architecture computing hardware, efficient memory and storage, and networking connections that allows the generation, storage and exchange of traffic flow. Therefore, the IT management is familiar with mitigations of cyber threats through years of experience. In fact, since IT architecture is commonly situated in headquarters and office settings, most of the funding have been invested in this sector.
On the contrary, OT systems are implemented at operating sites like PLCs, and ICS (industrial control systems) and SCADA. Traditionally, these proprietary assets were made to perform specific tasks and remotely isolated, and thus were not designed with security functions. In fact, OT systems are made to operate in a long life cycle and thus, there is still a considerable number of OT systems deployed decades ago. The sunk investment of OT makes it less favorable in budgeting for security measures. Therefore, when OT are also connected to the network, air gaps are closed and they have instantly become the targets for cyber malwares.
Requirements
To fully protect critical infrastructures from advanced cyber malwares, it is necessary to establish multi-layer protections covering both IT and OT segments. In a common digitalized setting for critical infrastructures, OT controls and manages level 0 to level 2 networks like instrumentation bus, controller LAN and supervisory HMI LAN, whereas the IT monitors and authenticates HQ and office based networks like web server, email server, FTP server and enterprise servers, which are favored by the managements. In a more advanced model, a DMZ (Demilitarized Zone) is established as an additional layer of protection towards externally interfaced services.
In order to protect digitalized and connected critical infrastructures today, it requires a well-converged architecture that can protect IT, OT and even the DMZ. Therefore, an Israel-based ICS cyber-security start-up contacted Lanner to collaborate for a hardware-software integrated solution with real-time monitoring visibility and policy-enforced control to protect critical facilities against malicious cyber attacks. In this collaboration, Lanner provides firewall hardware platforms that can fulfill the following requirements in ICS SCADA settings:
Lanner’s Converged IT/OT Cyber Security Solutions
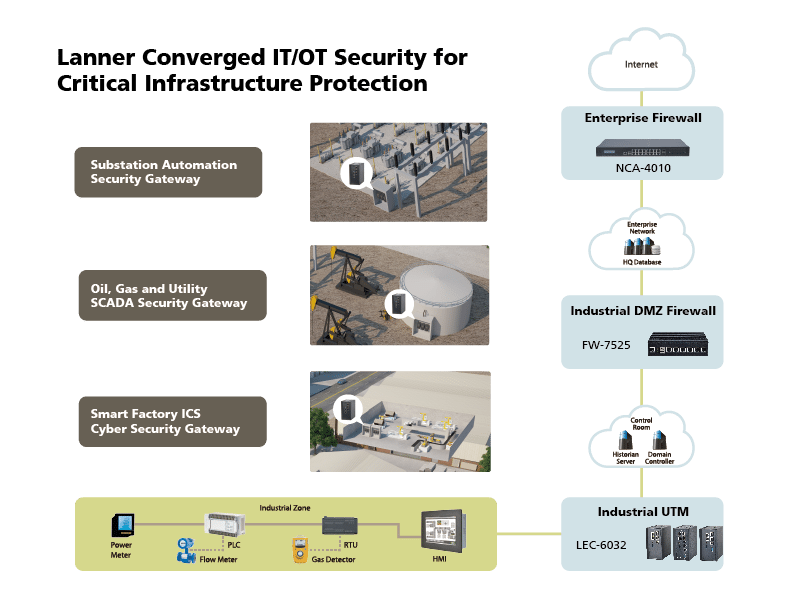
For aggregated Critical Infrastructure cybersecurity solution, Lanner introduces the integrated and converged solution pack includes the LEC-6032C as the rugged industrial UTM in OT, FW-7525 as the industrial DMZ firewall between IT and OT, and lastly NCA-4010 as the enterprise firewall for the IT segment.
LEC-6032 is selected to perform DPI, white list and virtual segmentation for the protection of assembly line servers, PLCs and SCADAs. LEC-6032 is ideal as next-generation firewall for the harsh OT environment due to its physical qualities such as fanless design, wide operating temperature range, and dual power path. Processor wise, LEC-6032 is driven by small-footprint Intel® Atom C3845 SoC for power efficiency at ICS and SCADA sites. In case of network disruption, LEC-6032 offers LAN Bypass fault-tolerant design to provide alternate traffic route.
FW-7525 is deployed in the industrial DMZ between IT and OT. Lanner’s FW-7525 is a valued pack of power-efficient multi-core Intel® Atom SoC, rich LAN I/O configurations, built-in cryptographic accelerator, and hardware-assisted AES-NI instructions. With these qualities, FW-7525 is the optimal UTM gateway for DMZ firewall to deeply inspect packets, monitor traffic and enforce security policies.
For the IT environment, Lanner selects NCA-4010 to perform DPI, white list and firewall tasks. This 1U rackmount appliance is empowered by server-level Intel® Xeon® D-1500 SoC and ECC-supported DDR4 memory. Bandwidth-wise, NCA-4010 supports up to sixteen RJ-45 GbE ports and two (2) 10G SFP+ ports. The bandwidth can be expanded by adding 1 Ethernet NIC module. Meanwhile, the 19” form factor of NCA-4010 makes it a space-efficient appliance for data centers today.
The deployments of next-generation firewalls: NCA-4010, FW-7525 and LEC-6032 in each IT, OT and DMZ respectively are aggregated to provide a well-converged Critical Infrastructure cybersecurity solution.


