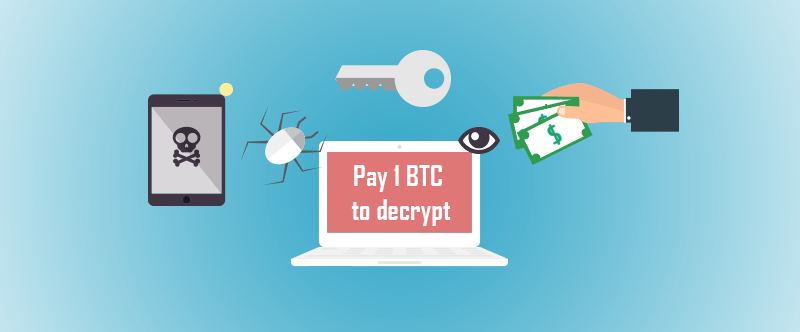
2016 was known as the year of ransomware, but 2017 is looking more and more dangerous for the IoT -and especially health care- as the malware continues to evolve. Patient healthcare systems are an alluring target to hackers seeking a quick buck, as many recent attacks have ended in facilities forking over the cash (bitcoins) to get their critical systems back online.
In response to improvements in cyber security, backup systems and fail safes which have made ransomware much less effective, hackers have been invigorating their tools with new goals and functionality.
Ransomware can learn new tricks
As the hackers targeting healthcare industries have shown, they’ve one goal: money; ethics and morals be damned. To those ends, advanced ransomware is being constantly updated with new functionality.
One such piece of ransomware (firecrypt) decided to expand its criminal activities to the DDoS game employing the resources available from ransomed machines to launch attacks on a 2nd victim. This shows how trivial it is for a malware authors to leverage other monetary tactics once a machine has been compromised.
Recent white-hat hacker demonstrations at the RSA show the sheer amount of insecure medical devices connected to the internet. But the scariest thing is how easy it is for malware to spread through a simple email
Old tricks find new life
In part due to several prominent attacks across the IT sector, security professionals currently have several viable ways to mitigate ransomware. Periodic backups to re-image affected systems, cloud storage technologies and strict security policies can all thwart hackers from profiting off of ransomware.
Nowadays, given the increasingly intrusive nature of IoT, ransomware has started shifting from file encryption back to it’s roots: device ransoming. Now instead of gambling on a lack of backups/or the backups being compromised themselves, hackers can ransom critical systems which can cause irreparable or costly damage in a short amount of time; thereby forcing victims to choose the less damaging option – paying the ransomers.
The weakest link in the chain of security
How does malware infiltrate networks? Believe it or not, the the majority of malware is still spread through emails. Not scary 0-day exploits, not malicious USBs, simple emails with malicious code embedded in some form or another. Known as phishing, the hacker sends out carefully crafted emails in an attempt to get the user to unwittingly run the code.
Aren’t next-generation firewalls the line of defense against these kinds of attacks?
Although we’d like to think that a NGFW will protect us old threats like email phishing, the reality of the matter is that hackers have the advantage in this area. Defensive software continually evolves, but so do the tools hackers employ – and at a much greater pace. In the end even layer 7 firewalls can only capture threats it knows about, so hackers exploit this to send malware to the easiest target in a corporate environment: the less technologically inclined employees.
Security-focused thinking
As is becoming increasingly apparent, clueless employees are very often the entry point for hackers. Training personnel in best security practices, and enforcing them along with a strict security policy will go a long way into preventing malware, data breaches and data leaks. Disabling unnecessary functionality, reducing complexity and implementing full network visibility are all modern practices that allow the best security systems to detect, respond and mitigate ongoing attacks
Augmentation/IoT implants future risks
Embedded technology gets smaller everyday, and as biomedical advancements continue to leverage technology, so will hackers. A future with augmented vision seems all well and good until hackers remotely disable it, or even worse, slightly alter it without your knowledge. Industry leaders and device manufacturers will have to band together to tightly integrate viable security in this volatile digital world. The healthcare industry will be one of the greatest benefactors of IoT, and with it come incredible responsibility to ensure the security of patient data, and most of all the patient himself.